Configuring an external identity provider
info
The Identity UI does not offer support for configuring external identity providers. You can configure an external identity provider directly in Keycloak Administrator Console.
To configure an external identity provider like OpenID Connect, SAML, LDAP, or Active Directory, take the following steps:
- Log in to the Keycloak Administrator Console. Open the URL you have configured for Keycloak in your browser.tip
When using the example Docker Compose setup, Keycloak is available at http://localhost:18080/.
- Click Administrator Console and log in using the Keycloak administrator credentials. The default administrator username is
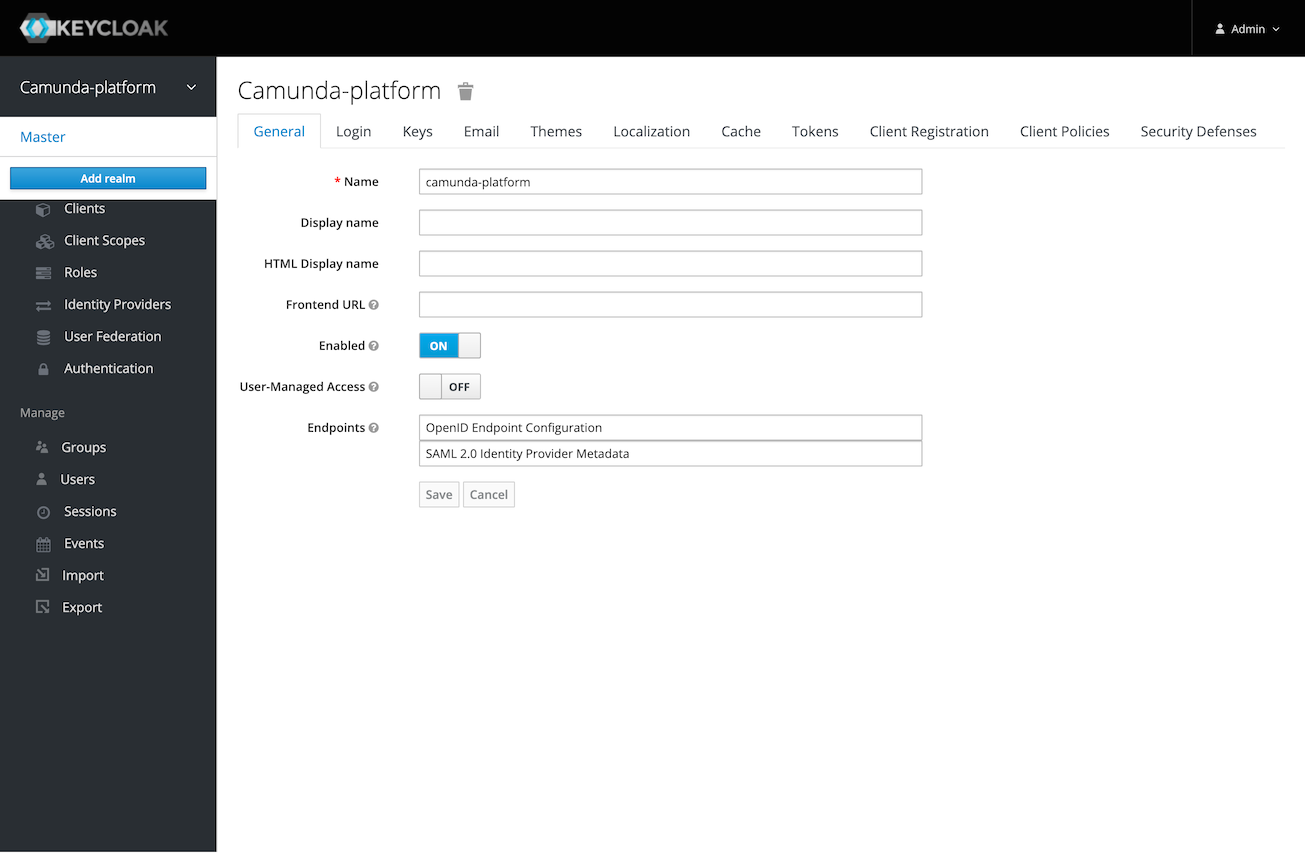
admin. When deploying Camunda 8 with Helm charts, you can extract the password as described in secrets extraction. Using the example Docker Compose setup, the password is set viaKEYCLOAK_ADMIN_PASSWORDenvironment variable and isadminper default. - Select the realm you are using with Camunda 8. By default, this is Camunda-platform.
- Add an identity provider using one of the following methods:
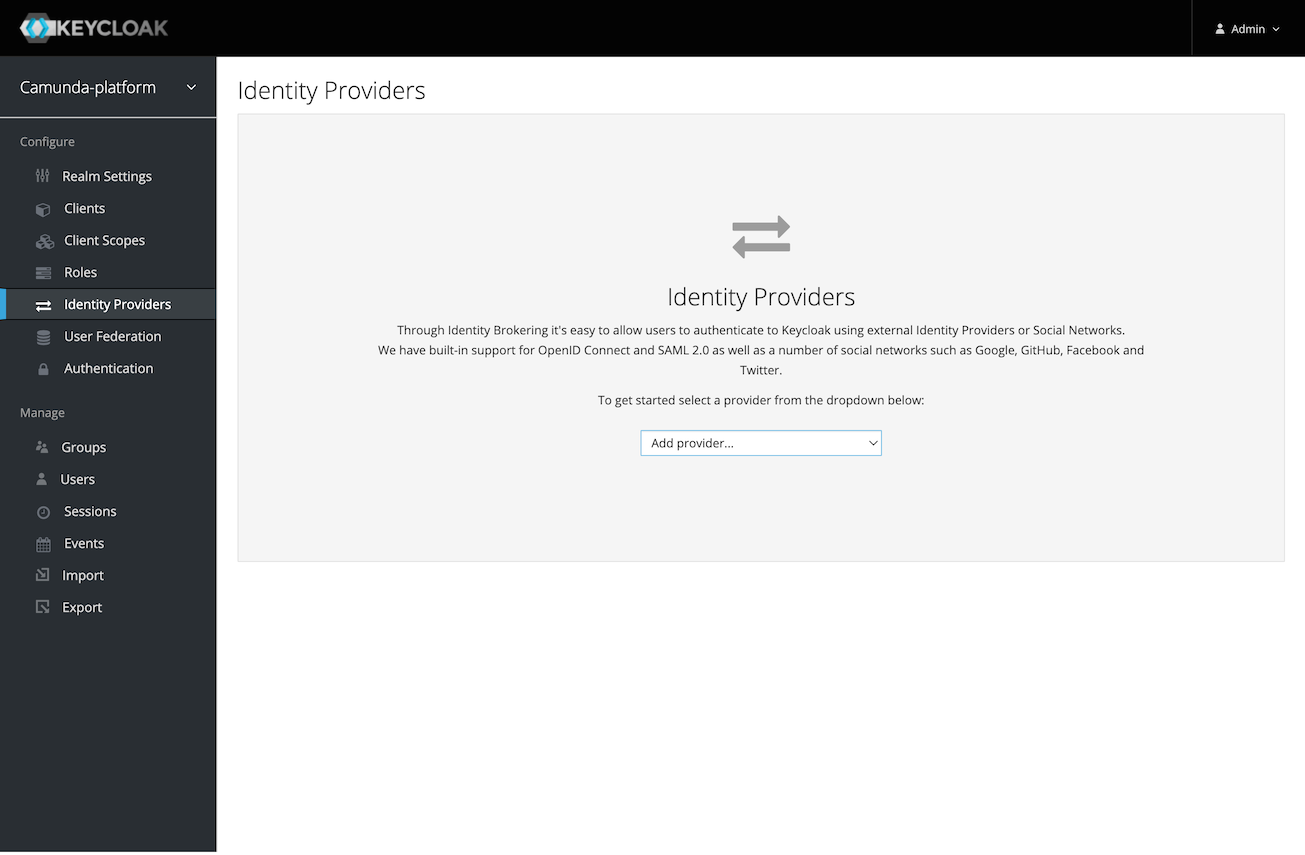
- To add an OpenID Connect or SAML provider, select Identity Providers in the main menu, click Add provider..., and fill in all required configuration settings.
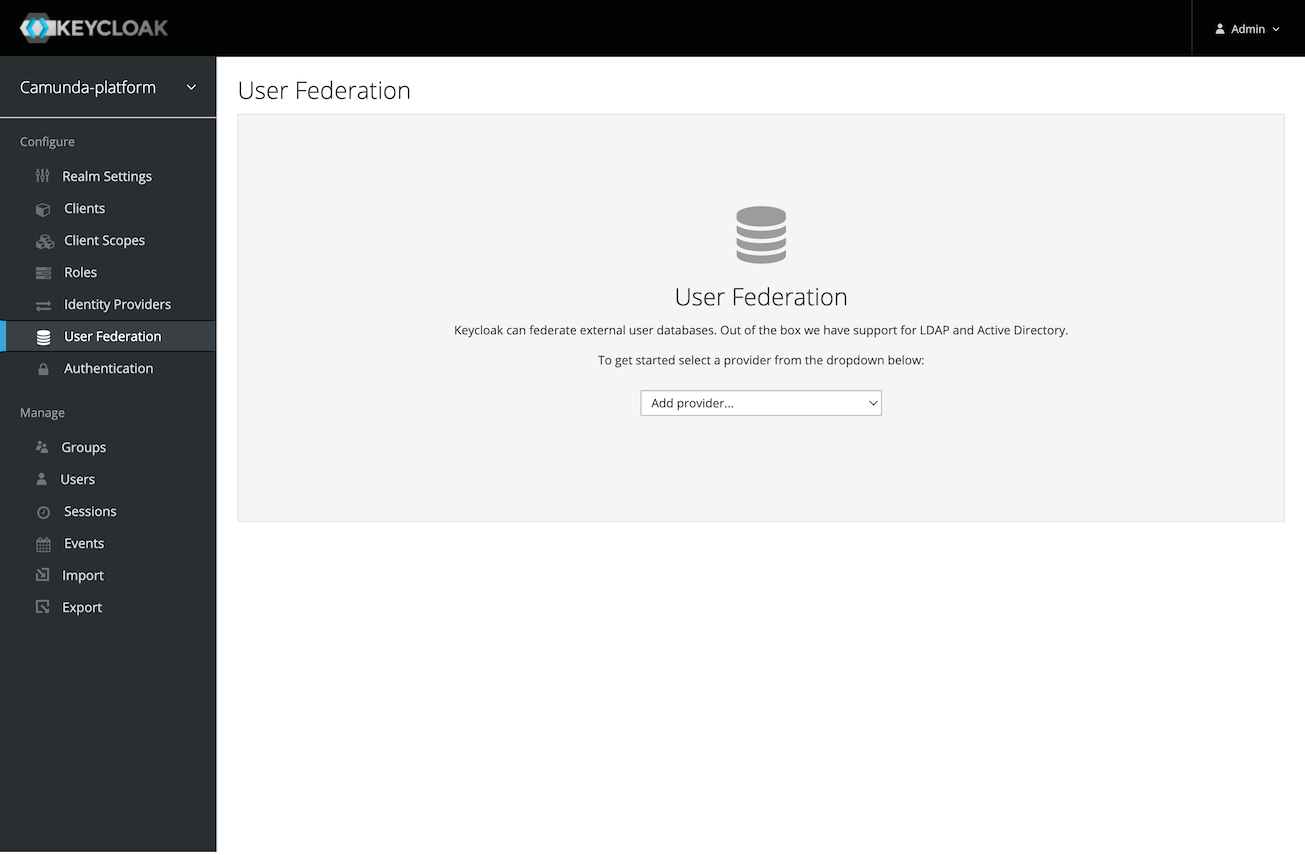
- To connect to your LDAP, Active Directory, or Kerberos server, select User Federation in the main menu, click Add provider..., and fill in all required configuration settings.
- To add an OpenID Connect or SAML provider, select Identity Providers in the main menu, click Add provider..., and fill in all required configuration settings.
tip
Keycloak supports a wide variety of authentication options, such as mapping external user groups, roles, or scopes to internal roles, and configuring the login screen and flow when multiple providers are added.
Visit the Keycloak documentation for details on adding a provider, configuring authentication, and integrating identity providers.