Amazon Bedrock AgentCore Runtime connector
With the Amazon Bedrock AgentCore Runtime outbound connector, you can invoke external agents deployed on Amazon Bedrock AgentCore Runtime from your BPMN process.
Use this connector to delegate complex reasoning tasks to specialized AI agents hosted on AWS, such as fraud detection, risk analysis, or document processing agents built with frameworks like Strands, LangGraph, or CrewAI.
Prerequisites
To use the Amazon Bedrock AgentCore Runtime connector, you need the following:
- An AWS account with an access key and secret key, or a configured default credentials chain.
- An agent deployed to AgentCore Runtime in an
ACTIVEstate. - IAM permissions to execute the
InvokeAgentRuntimeaction on the agent's ARN.
Learn more about AgentCore Runtime in the official documentation.
Use Camunda secrets to store credentials and avoid exposing sensitive information directly from the process. Refer to managing secrets to learn more.
Create an Amazon Bedrock AgentCore Runtime connector task
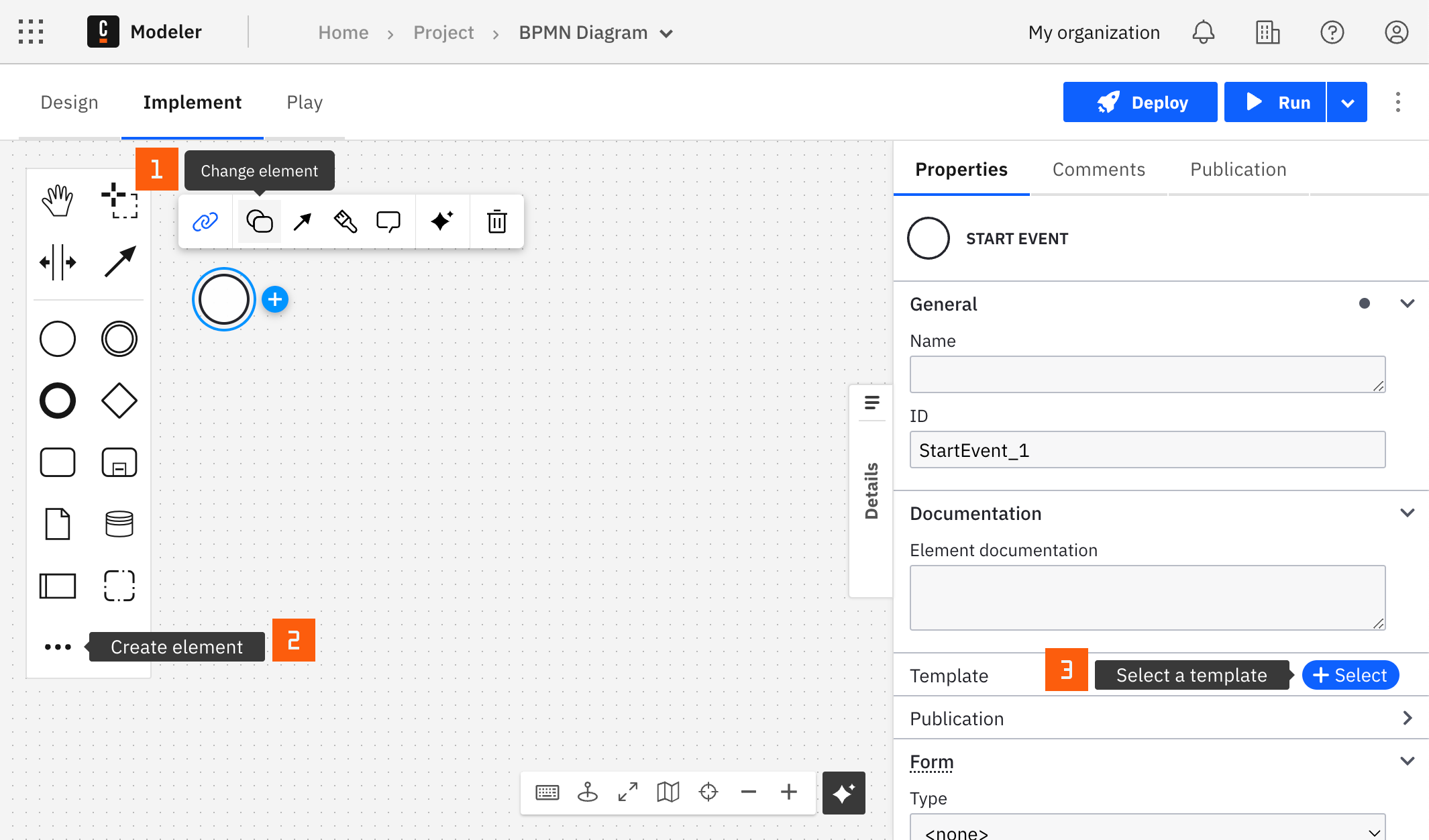
You can apply a connector to a task or event via the append menu. For example:
- From the canvas: Select an element and click the Change element icon to change an existing element, or use the append feature to add a new element to the diagram.
- From the properties panel: Navigate to the Template section and click Select.
- From the side palette: Click the Create element icon.
After you have applied a connector to your element, follow the configuration steps or see using connectors to learn more.
Authentication
To authenticate, choose one of the methods from the Authentication dropdown. The supported options are:
- Use Credentials if you have a valid pair of access and secret keys provided by your AWS account administrator.
This option is applicable for both SaaS and Self-Managed users.
- Use Default Credentials Chain if your system is configured as an implicit authentication mechanism, such as role-based authentication, credentials supplied via environment variables, or files on target host. This approach uses the Default Credential Provider Chain to resolve required credentials.
This option is applicable only for Self-Managed or hybrid distributions.
For more information on authentication and security in Amazon Bedrock, see Amazon Bedrock security and privacy.
Configuration
In the Region field, enter the AWS region where your AgentCore Runtime agent is deployed. For example, us-east-1.
Action
The Amazon Bedrock AgentCore Runtime connector supports the following action.
Invoke agent runtime
Parameters
| Parameter | Required | Description |
|---|---|---|
| Agent Runtime ARN | Yes | The ARN of the deployed AgentCore Runtime agent. You can find it in the AgentCore console or in the output of agentcore deploy. |
| Prompt | Yes | The message or task to send to the agent. Supports FEEL expressions. |
| Session ID | No | An optional session ID for multi-turn conversations. When provided, the agent retains context from previous interactions within the same session. |
Response
The connector returns the following fields:
| Field | Description |
|---|---|
response | The agent's response text or payload. |
sessionId | The runtime session ID. Use this value in subsequent calls to continue the conversation. |
statusCode | The HTTP status code of the response. |
Output mapping
- Use Result Variable to store the response in a process variable. For example,
agentResult. - Use Result Expression to map specific fields from the response into process variables.
For example, to extract the agent's response:
= {
answer: response,
session: sessionId
}
Example: Invoke a fraud detection agent
Configuration:
- Agent Runtime ARN:
arn:aws:bedrock-agentcore:us-east-1:123456789012:runtime/fraud_agent-1GRoTlCtHi - Prompt:
Claim: Customer reports stolen vehicle worth $45,000. Filed 2 days after policy activation. No police report.
Response:
{
"response": "{\"result\": {\"role\": \"assistant\", \"content\": [{\"text\": \"{\\\"riskScore\\\": 85, \\\"riskLevel\\\": \\\"HIGH\\\", \\\"flags\\\": [\\\"Policy activated only 2 days before claim\\\", \\\"No police report filed\\\", \\\"High-value claim\\\"], \\\"recommendation\\\": \\\"REJECT\\\"}\"}]}}",
"sessionId": "76f079e6-f30b-4416-9fbc-5d09d2ad31de",
"statusCode": 200
}
Multi-turn conversations
To maintain context across multiple interactions with the same agent, pass the sessionId from the previous response into the Session ID field of the next call. This allows the agent to remember prior messages and maintain state.
When using the connector as a tool in an AI Agent Sub-process, use the fromAi() function for the Prompt field to let the orchestrating agent compose the message dynamically based on the user's request.